|
Producer: ACSYS BSC Limited
Modules: DEM Server
(includes Sybase SQL Anywhere 8.0.3); DEM Client
DEM
integrates with: Crime Workbench,
Stellent IBPM.
Data Entry Module
(DEM) is designed to enter information to the
following ALERT system databases:
The data can be entered to both systems via HTML forms
respective for each of the databases, either independently or in an integrated
way. The created documents are stored in a built-in local database. They can
also be managed and searched for from within the data entry workstation. The
local database enables to distinguish the time and date of document creation
from the time it was sent and allows for viewing the contents of the documents
which have already been sent. Each document is provided with the following
system data:
Documents can be directly transferred to target databases via
a computer network. The possibility to transfer them between the data entry
workstations on portable media such as CD or flash memory card is also provided.
This allows you to create documents on the workstations which are not connected
to the computer network and then transfer them to the target system via data
entry workstations provided with such connections.
Data transfer via the computer network is performed with HTTP
and HTTPS protocols, with the use of port numbers 80 and 443. This allows you to
use the program without the need to reconfigure the access protection software,
such as firewalls.
Data transmission can be either hardware or software encoded.
The hardware devices used for this purpose are encoding cards. Software encoding
makes use of the algorithms implemented by SSL protocol, enabled by Microsoft
Internet Information Services.
The program provides for the option to select the data
transmission mode which applies the authorization mechanism for the users who
send documents.
Confirmation mechanism and control sum checking provide for
the completeness of the transmission (the document which has been send partially
is rejected and needs to be send once again).
Supported Databases and Basic
Features
The DEM module supports
the following ALERT system databases:
The module allows
you to enter the data in the form of reports and two kinds of
attachments enclosed to the reports. The textual data can be entered via the
keyboard or captured from other sources together with sound or image data.
The textual data entered via the keyboard with respective
data entry forms can be split into the two following groups:
-
(a) reports, memos and other documents which become
source records in Crime Workbench databases;
-
(b) details on entities such us persons, vehicles,
addresses, organizations or phones which become analytical records in
Crime Workbench databases.
The details on analytical entities (b) are always attachments
linked to information reports which they are based on (a) and this relation is
preserved in Crime Workbench databases.
The other kind of attachments to information reports are
image, sound or other textual data which is sent to
Stellent IBMP electronic archives after indexing.
The DEM module also allows
to directly enter the images of documents from scanners provided with TWAIN
interface.
The basic features of the DEM
module include:
-
simultaneous handling of many Crime Workbench
criminal analysis databases installed on one server;
-
simultaneous handling of many
Stellent IBMP electronic archives within one
IBMP domain;
-
possibility to create integrated documents
including both textual part, stored in Crime Workbench, and other parts, such as
image or sound data, stored in IBMP
electronic archives;
-
compatibility to scanners provided with TWAIN
interface;
-
store documents and information on the current
status of documents in a local built-in database;
-
encoded data transmission to target databases
via computer networks;
-
possibility to export documents (packages)
created on data entry workstations with no access to computer network to
portable data carriers, transfer them to the workstations provided with such
connection and send them to target systems therefrom;
-
management of documents stored in local
built-in database with the use of folder structure;
-
searching for documents stored in the local
database;
-
audit functions;
-
automatic update of configuration files and
releases on data entry workstations.
Schematic Diagram
The DEM module includes
two basic applications which are the DEM
Client and the
DEM Server. They communicate with each
other via the TCP/IP network.
The DEM
Client is installed on data entry
workstations and allows you to enter data as well as create, edit, send and
manage documents.
The DEM
Server is installed on the workstation linked
to a protected LAN and its role is to receive documents, sending receipt
messages to DEM
Client and placing documents in target databases.
Below please find the main dialog of the
DEM Client.
You can see the folder structure, which enables document management, on the left
and the data entry form on the right.
The DEM
Client includes the following two basic
components:
-
The application of the Microsoft Windows which
provides graphical environment to handle all the functions provided at the data
entry workstation.
-
Access database used to store
documents and all the other information related to these documents.
The DEM
Server includes the following three basic
components:
-
DEM
Listener, which co-operates with a web server. Its role is to provide for
communication with data entry workstations, receive documents and transfer them
to the intermediary database.
-
DEM
Intermediary Database, which is Sybase SQL Anywhere. Its role is to store the
received documents before they are transferred to the target system.
-
DEM
Main application component, whose role is to periodically search the
DEM Intermediary Database for received
documents and send them to the target system. The DEM Main connects to Crime Workbench Server or Stellent IBMP Server.
The communication with Crime
Workbench Server is performed via a shared disk folder and exchange
files. The files are automatically imported to Crime
Workbench with the use of Crime Workbench
Importer. The communication with Stellent IBMP
is performed via the TCP/IP protocol.
The DEM Main runs as
Microsoft Windows service.
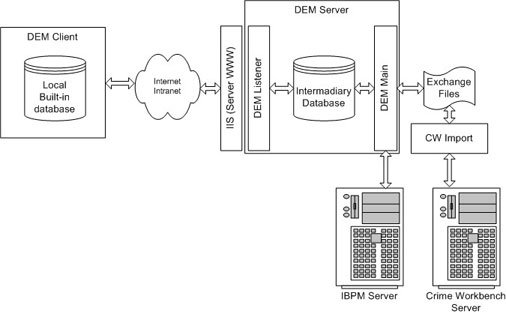
Schematic Diagram of Data Entry Module.
Storing and Searching for
Documents
The created documents are stored in the local built-in
database, which is the part of the DEM
Client. You can create your own folder
structure to manage the documents by placing them in appropriate folders.
After the documents are sent to the
DEM Server and the receipt message is
received you can delete documents from the database.
The local built-in database allows you to search for the
documents on the basis of the following criteria:
-
document ID;
-
document status (e.g.: New, Ready for Sending,
Sent, Saved, Deleted);
-
log IDs of users working with documents
(operations such as create, modify, send, export or import documents);
-
date and time of performing operations on
documents (create, modify send, export or import dates);
-
used in the document summary (the string
of first 128 characters of the documents contents);
-
grouping documents within export/import
packages.

Search Dialog
Entering Data from
Non-Networked Workstations
The DEM module provides
the possibility to enter data to the ALERT system from the entry workstations
which are not linked to the DEM
Server via the computer network. You can
create documents on a non connected workstation and make use of the Import
function, which encodes selected documents and saves them on indicated portable
media, such as CD or flash cards. The media can be then transferred and read at
another workstation, provided with network connection, with the use of Import
function. The Import function decodes the documents and saves them in the local
built-in database.
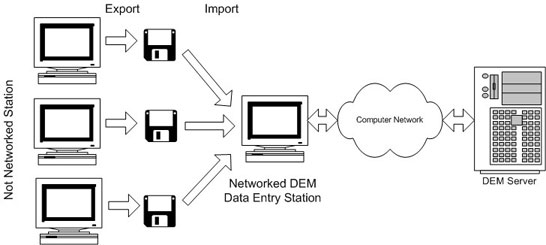
Transferring Documents with Export/Import Functions
The documents exported from standalone workstations and
imported to the networked workstation are provided with additional information
regarding individual packages of documents, i.e. all documents exported at one
turn. This information includes the following data:
User Identification and
Authorization
The DEM module does not
provide authorization for individual operations performed within the
application, such as create edit or search for documents. This means that anyone
who is granted access to the program is simultaneously granted the access to all
documents stored in the local built-in database and all functions provided by
the application.
Authorization is optionally required to start the data
transmission between the DEM
Client and the
DEM Server. This option is controlled
from the level of system’s administrator. The default setting is that the user
is required to enter the name and password. The authorization mechanism can be
replaced (requires additional authorization software) with another one which can
be based on, for example, chip card identification.
The application stores the IDs of the users who worked with a
given document. The individual operations performed and their time is also
respectively recorded per document. The following information is recorded in
this respect:
-
creation of the document;
-
last modification;
-
sending the document to the
DEM Server
via the computer network;
-
exporting to portable media;
-
importing from portable media to networked data
entry workstation.
Data Encoding
The documents stored in local built-in databases on the data
entry workstations are not encoded. They are encoded for the needs of data
transmission between the DEM
Client and DEM
Server and when exporting from a non
networked data entry workstation to portable data carriers.
The following encoding methods are available:
Makes use of Microsoft Windows symmetric encoding algorithms.
Encoding keys are stored in protection dongle memory. Each data entry
workstation is provided with individual protection dongle.
Concerns only data transmission via the computer network.
Requires a certificate of a public key (asymmetric encoding) to be installed on
the web server which co-operates with the DEM
module. The Microsoft IIS encoding algorithms, including 128 bit key encoding,
are used.
Concerns only data transmission via the computer network.
Requires specialized network transmission encoding cards.
Protection Dongles
The DEM module is
protected with dongles (USB and Centronix port options available). You cannot
open the application without the dongle.
The dongle additionally performs the following functions:
Unique four-character identifier stored in the dongle memory
is automatically amended to each document created on the workstation. This
enables to determine the original workstation on which the document has been
created.
Document counter is stored and automatically updated in the
dongle memory. Each document is given a unique number which, combined with the
workstation identifier, enables to identify the document within the whole
system. As the counter is within the dongle, the damage or replacement of the
data entry workstation have no impact on identification.
Keys and passwords used by encoding/decoding algorithms are
stored in the dongle memory.
|